Creating a shorter URL assistance is an interesting job that involves a variety of facets of software program growth, which include Net progress, databases administration, and API layout. Here's an in depth overview of the topic, by using a give attention to the necessary components, problems, and ideal practices involved with developing a URL shortener.
1. Introduction to URL Shortening
URL shortening is a technique on the net during which a long URL could be converted right into a shorter, additional workable kind. This shortened URL redirects to the initial very long URL when visited. Providers like Bitly and TinyURL are very well-recognised samples of URL shorteners. The need for URL shortening arose with the advent of social networking platforms like Twitter, exactly where character restrictions for posts built it challenging to share prolonged URLs.
Create QR
Over and above social networking, URL shorteners are valuable in advertising strategies, emails, and printed media exactly where very long URLs might be cumbersome.
two. Core Components of a URL Shortener
A URL shortener generally contains the subsequent factors:
Internet Interface: This can be the front-conclude portion wherever buyers can enter their extended URLs and get shortened variations. It can be a simple variety with a Website.
Databases: A databases is essential to retail outlet the mapping involving the first very long URL and also the shortened Edition. Databases like MySQL, PostgreSQL, or NoSQL possibilities like MongoDB can be utilized.
Redirection Logic: Here is the backend logic that usually takes the shorter URL and redirects the consumer to your corresponding prolonged URL. This logic is usually carried out in the internet server or an application layer.
API: Several URL shorteners present an API making sure that 3rd-party purposes can programmatically shorten URLs and retrieve the original long URLs.
three. Planning the URL Shortening Algorithm
The crux of a URL shortener lies in its algorithm for converting a protracted URL into a brief just one. Several techniques is often employed, which include:
authenticator microsoft qr code
Hashing: The long URL can be hashed into a set-dimensions string, which serves because the quick URL. Nonetheless, hash collisions (diverse URLs leading to precisely the same hash) should be managed.
Base62 Encoding: One frequent technique is to employ Base62 encoding (which takes advantage of sixty two figures: 0-nine, A-Z, in addition to a-z) on an integer ID. The ID corresponds to your entry in the databases. This technique makes certain that the limited URL is as quick as is possible.
Random String Era: Yet another tactic is usually to deliver a random string of a hard and fast size (e.g., 6 figures) and Look at if it’s by now in use within the databases. Otherwise, it’s assigned to your very long URL.
four. Database Administration
The database schema for just a URL shortener is often straightforward, with two Principal fields:
نظام باركود للمخازن
ID: A novel identifier for each URL entry.
Extended URL: The original URL that needs to be shortened.
Short URL/Slug: The small Variation on the URL, often stored as a singular string.
Together with these, you might like to retailer metadata such as the development date, expiration day, and the amount of times the shorter URL has actually been accessed.
5. Handling Redirection
Redirection is usually a critical Component of the URL shortener's Procedure. Whenever a person clicks on a short URL, the company should quickly retrieve the initial URL within the database and redirect the person employing an HTTP 301 (long term redirect) or 302 (momentary redirect) status code.
باركود منتج
Effectiveness is vital in this article, as the method should be just about instantaneous. Procedures like database indexing and caching (e.g., working with Redis or Memcached) may be utilized to hurry up the retrieval procedure.
six. Stability Factors
Protection is a significant problem in URL shorteners:
Destructive URLs: A URL shortener is usually abused to spread malicious inbound links. Implementing URL validation, blacklisting, or integrating with third-social gathering stability services to check URLs ahead of shortening them can mitigate this possibility.
Spam Avoidance: Rate limiting and CAPTCHA can avoid abuse by spammers seeking to deliver A large number of quick URLs.
7. Scalability
Since the URL shortener grows, it might require to take care of many URLs and redirect requests. This demands a scalable architecture, possibly involving load balancers, distributed databases, and microservices.
Load Balancing: Distribute traffic across multiple servers to handle high loads.
Dispersed Databases: Use databases that can scale horizontally, like Cassandra or MongoDB.
Microservices: Different fears like URL shortening, analytics, and redirection into distinctive products and services to further improve scalability and maintainability.
eight. Analytics
URL shorteners typically supply analytics to track how frequently a brief URL is clicked, the place the targeted traffic is coming from, and also other beneficial metrics. This demands logging each redirect And maybe integrating with analytics platforms.
9. Conclusion
Building a URL shortener will involve a combination of frontend and backend advancement, databases management, and attention to protection and scalability. When it might seem like an easy company, making a robust, successful, and secure URL shortener offers a number of worries and calls for careful setting up and execution. Regardless of whether you’re creating it for personal use, interior organization applications, or like a general public services, being familiar with the underlying rules and best procedures is important for success.
اختصار الروابط
 Rick Moranis Then & Now!
Rick Moranis Then & Now! Yasmine Bleeth Then & Now!
Yasmine Bleeth Then & Now! Sydney Simpson Then & Now!
Sydney Simpson Then & Now!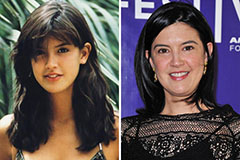 Phoebe Cates Then & Now!
Phoebe Cates Then & Now! Daryl Hannah Then & Now!
Daryl Hannah Then & Now!